Hello everyone! This challenge on TryHackMe has a difficulty rating of medium. Depending on your experience, it may feel easier or harder. You’re currently working as a T1 Security Analyst for an MSSP investigating alerts: Misc activity, A Network Trojan Was Detected, and Potential Corporate Privacy Violation.
Typically, such alerts would originate from an IDS or IPS, but in this case, you must manually verify whether they are true positives or false positives.
Once you spawn the provided machine, you’ll find a Tools directory and a Zone2.pcap file on the desktop.
Open Wireshark (Applications → Wireshark → File → Open) and load the PCAP to begin analysis.
I started with Wireshark to spot anything suspicious before touching Brim or Network Miner — and indeed, I found something: an IP address that downloaded an odd-looking file. Right-click packet #6 and select Follow → HTTP Stream to inspect the full transfer sequence.
Next, we’ll go through the challenge questions step by step.
Investigation Process
For the first two questions, I used Brim — a fantastic tool for packet analysis that I plan to use more at work.
Launch it from the Applications menu or via terminal. Once open, drag in Zone2.pcap and search using the IP you observed in Wireshark (from packet #6).
You’ll see the alerts populate. Double-clicking any of them opens a detailed alert view.
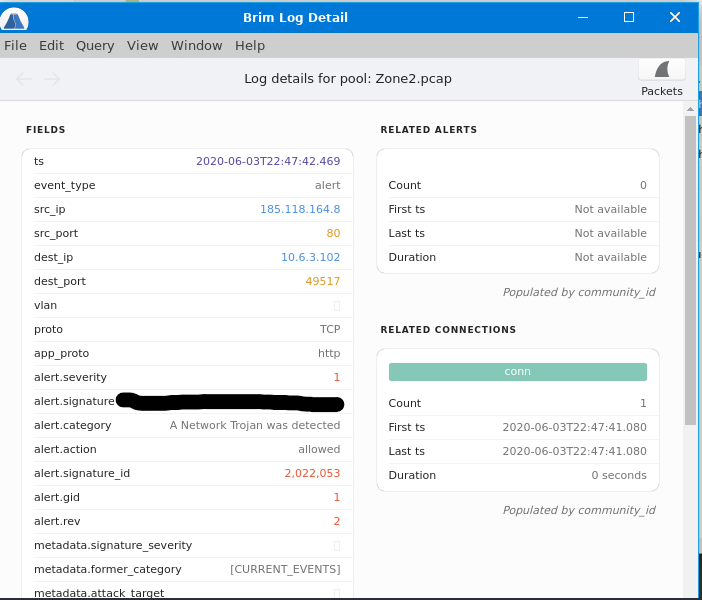
- Q1. What was the alert signature for “A Network Trojan was Detected”?
Ans: ET MALWARE Likely Evil EXE download from MSXMLHTTP non-exe extension M2
- Q2. What was the alert signature for “Potential Corporate Privacy Violation”?
Ans: ET POLICY PE EXE or DLL Windows file download HTTP
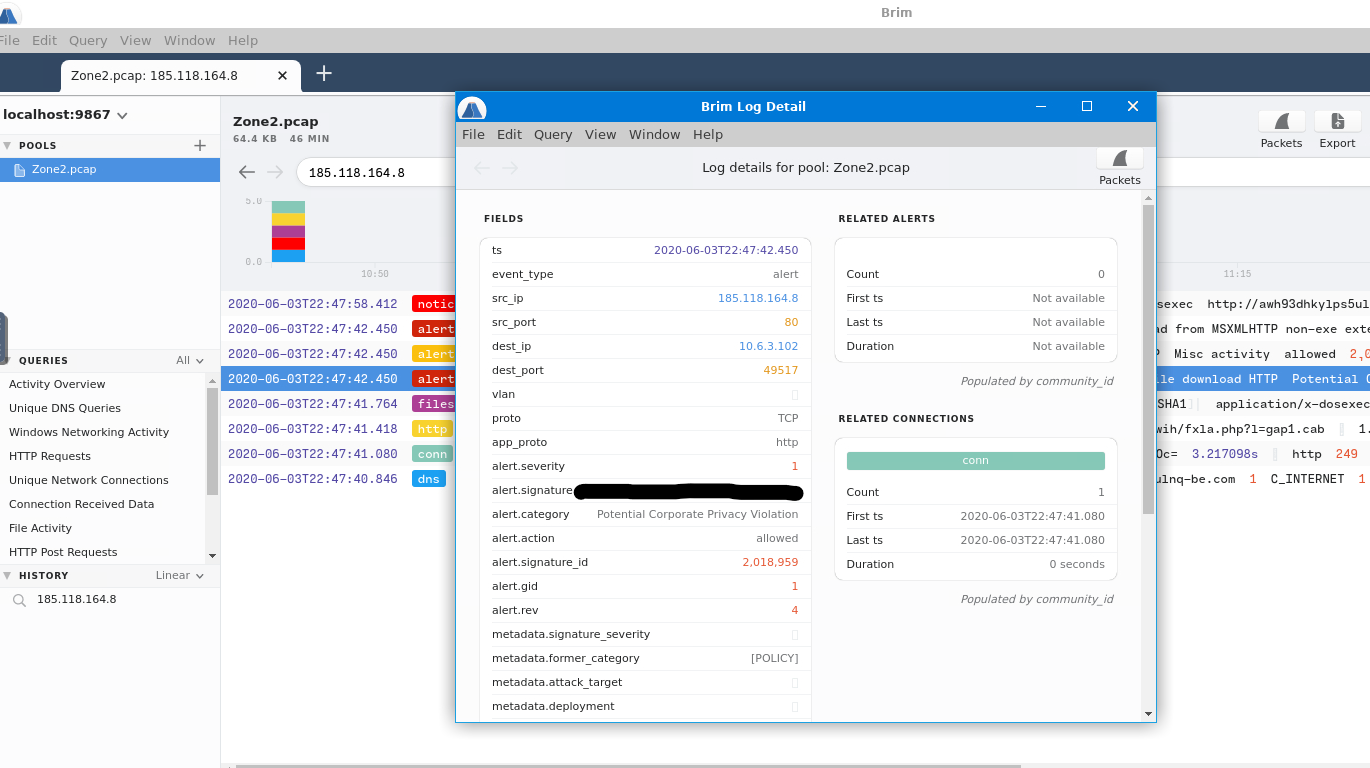
- Q3. What was the IP that triggered either alert (defanged)?
Ans: 185[.]118[.]164[.]8
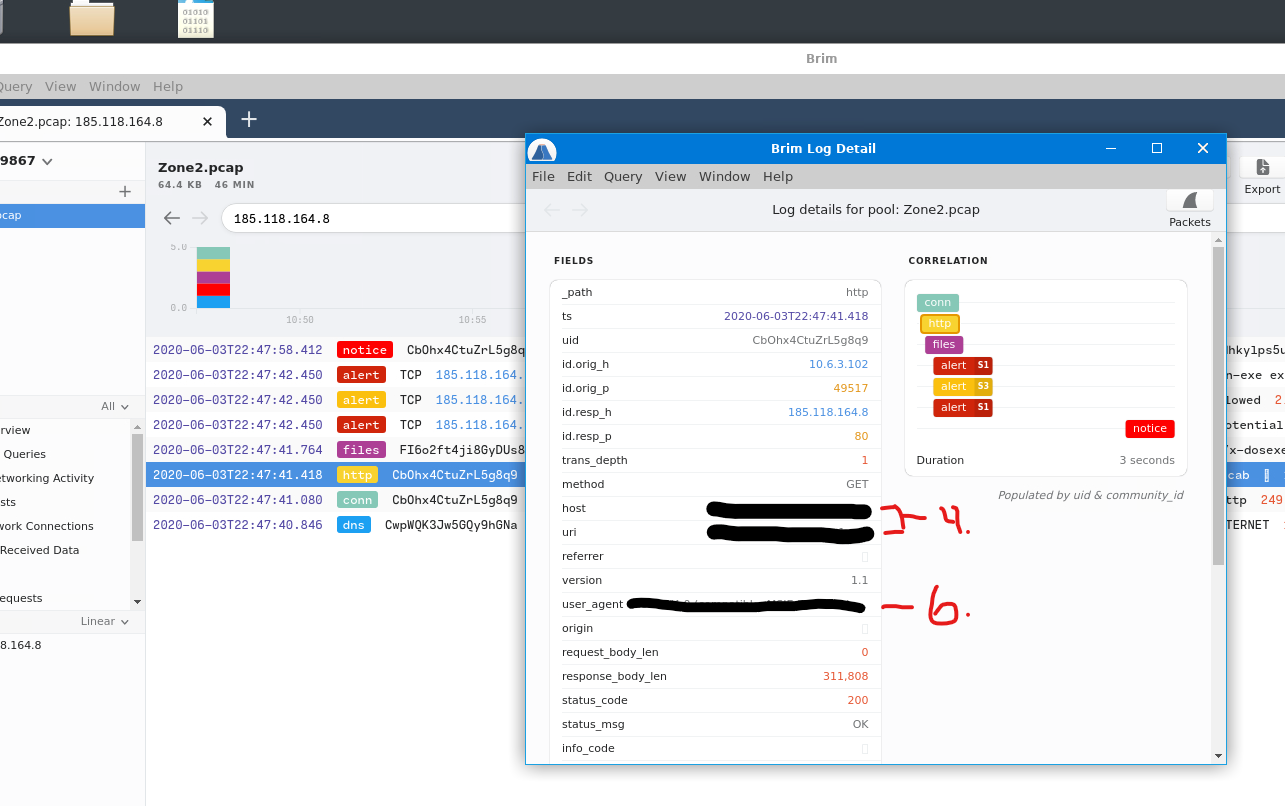
- Q4. Provide the full URI for the malicious downloaded file (defanged).
Ans: awh93dhkylps5ulnq-be[.]com/czwih/fxla[.]php?l=gap1[.]cab
- Q5. What is the name of the payload within the CAB file?
Ans: draw.dll
- Q6. What is the User-Agent associated with this network traffic?
Ans: Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 10.0; WOW64; Trident/8.0; .NET4.0C; .NET4.0E)
sha1sum <filename>
method=="GET" | cut ip, host, status_code- Q7. What other domains were labeled as malicious by VirusTotal? (alphabetical, defanged)
Ans: a-zcorner[.]com, knockoutlights[.]com
- Q8. Which IPs were flagged as Not Suspicious Traffic? (defanged, numerical order)
Ans: 64[.]225[.]65[.]166, 142[.]93[.]211[.]176
- Q9. For the first IP flagged as Not Suspicious Traffic, what malicious domains are associated with it? (defanged, alphabetical)
Ans: safebanktest[.]top, tocsicambar[.]xyz, ulcertification[.]xyz
- Q10. For the second IP, what domain appeared in network traffic (defanged)?
Ans: 2partscow[.]top
replace-with IP Addr | cut query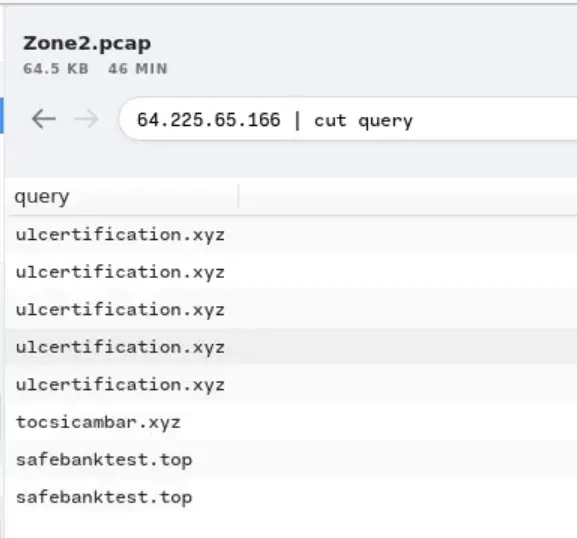
I know this was a lengthy write-up — but Warzone2 is a long challenge. It’s also one of the best examples of connecting alerts, packets, and external intel.
Huge thanks to ujohn for creating it.
Happy hacking!
