🧙 The Lore
In the storm-battered depths of a discreet mountain range lies ProtoVault, an arcane sanctuary guarded by the Everbound Order. Its defenses are sealed with runes that demand the blood, breath, and soulprint of their masters.
But magic can’t guard everything. A ransom scroll claims access to the Corespell and demands:
“Surrender the Archivist Verin.”
You, a skilled codecaster summoned by AnchorHelm, must prevent total cyber collapse.
🕵️♂️ Step-by-Step Analysis
1) Leak Origin: Connection String
The application code revealed a PostgreSQL connection string in plaintext, found in the Flask configuration:
app.config['SQLALCHEMY_DATABASE_URI'] =
'postgresql://assetdba:86d31d2207ec1debaafd806822122250@pgsql_prod_db01.protoguard.local/pgamgt?sslmode=verify-full'2) File Responsible for the Leak
Inspecting Git logs and source files identified the backup script responsible for the exposure.
app/util/backup_db.pyThis script SSHs into a DB host, dumps data, encodes via ROT13, and uploads to an Amazon S3 bucket.
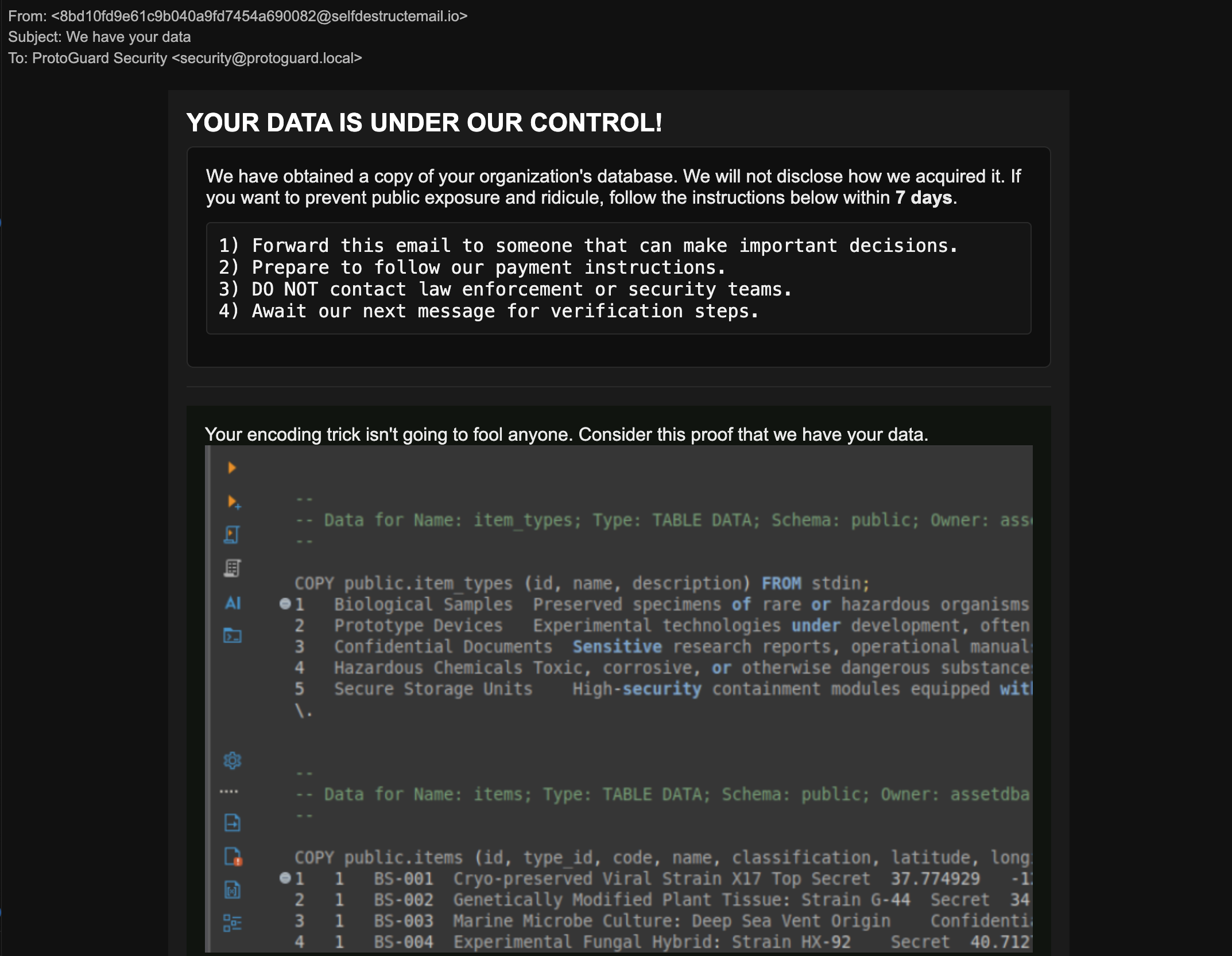
3) Leaked Data Discovery
Decoding db_backup.xyz from S3 revealed a password hash for Naomi Adler:
pbkdf2:sha256:600000$YQqIvcDipYLzzXPB$598fe450e5ac019cdd41b4b10c5c21515573ee63a8f4881f7d721fd74ee43d594) Public Leak Address
Despite S3 appearing private, the ROT13-obscured object was publicly reachable at:
https://protoguard-assets-management.s3.us-east-2.amazonaws.com/db_backup.xyz📸 Evidence & Screenshots

🧩 Conclusion
This scenario showcases real-world issues: poor secret management, cloud misconfiguration, and insecure scripting. Lessons: audit secrets, secure buckets, and monitor backup jobs.